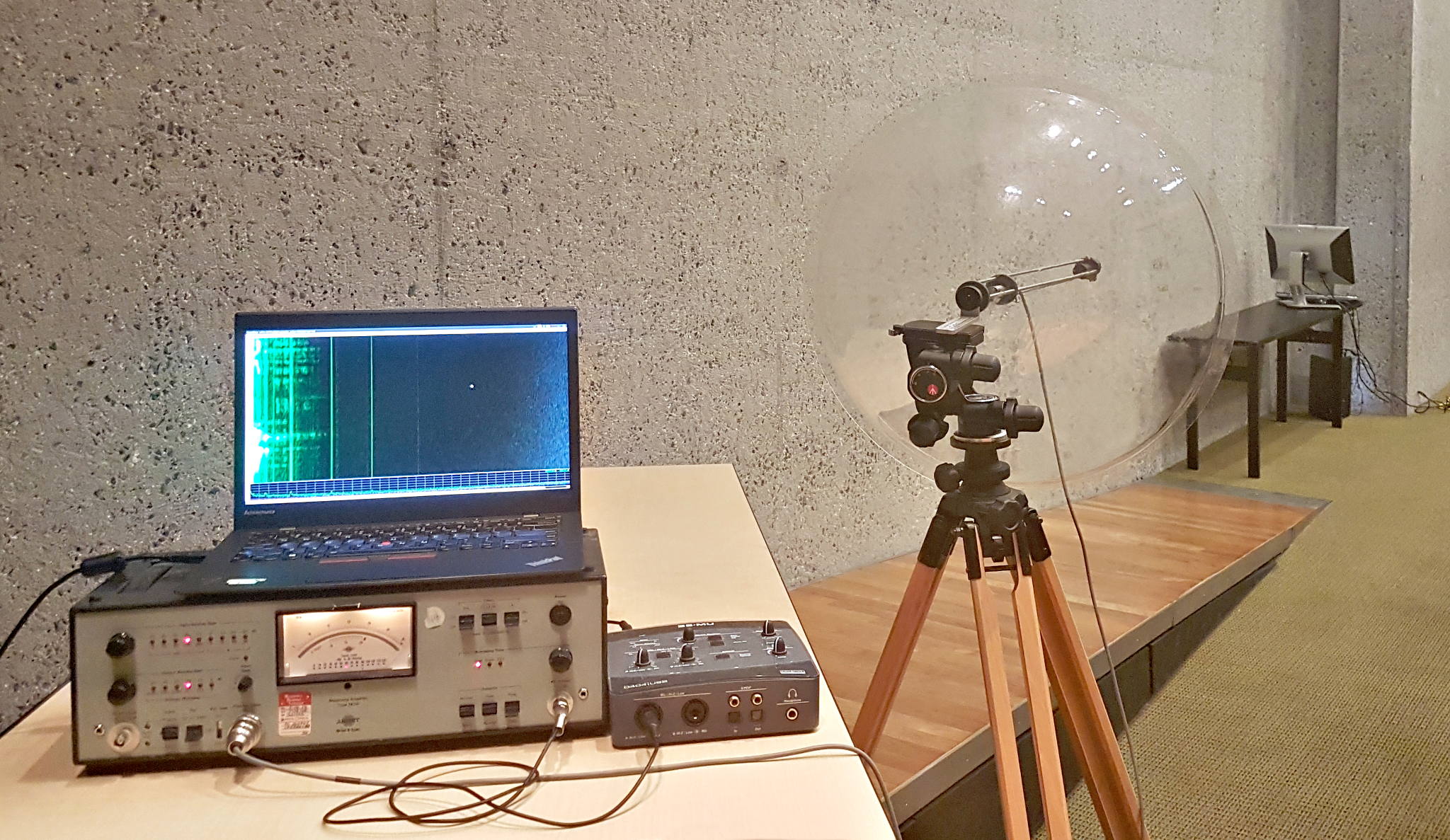
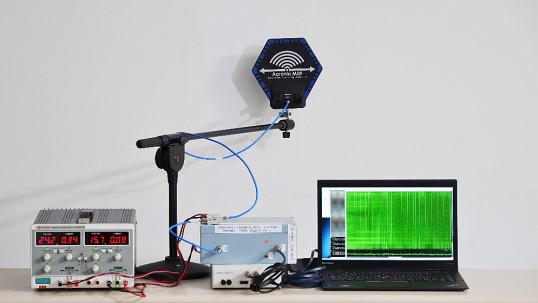
I don't quite remember where I first encountered the idea of Van Eck phreaking. Probably a blog in some sense related to cybersecurity, although the topic is not quite in that general domain. The name is derived from the Dutch PTT researcher Wim van Eck, who in 1985 published an unclassified technical demonstration which displayed a TV set reconstructing the screen content from a CRT monitor hundreds of meters away, using components that cost less than $15. The phenomenon itself was however widely known by intelligence agencies since at least World War II. Bell Labs had detected teletype cipher leakage in 1943, but van Eck's paper brought proper attention to the subject.
If it is still unclear, the act of VEP is compromising emanations from electronic equipment. All electronic equipment radiates signals that are correlated with its internal state. It is the information in those signals that is susceptible to being targeted while leaving no forensic trace on the target.
See Also
- Side-Channel Taxonomy (Placeholder)
- Soft TEMPEST Duality (Placeholder)
- Air-Gap Security and Covert Channels (Placeholder)
Notes
- Why van Eck's 1985 paper was politically subversive, not merely technical (Placeholder)
- Soft TEMPEST as a steganographic primitive (Placeholder)
- The signal-to-noise reformulation: why van Eck phreaking is fundamentally an information-theoretic problem (Placeholder)
- How Deep-TEMPEST's success implies the threat model must include ML-equipped adversaries (Placeholder)
- RAMBO and the philosophy of air-gap security (Placeholder)
- The connection between TEMPEST and EMC regulation (Placeholder)
- Why "Screaming Channels" represents a phase transition in the threat model (Placeholder)
- The keyboard as the highest-value van Eck target today (Placeholder)
To Read
Primary Source Material
- Wim van Eck, Electromagnetic Radiation from Video Display Units: An Eavesdropping Risk?, Computers & Security 4:269-286, 1985
- NSA, TEMPEST: A Signal Problem, Cryptologic Spectrum (Vol. 2, No. 3, 1972; Declassified 2008)
- Markus G. Kuhn & Ross J. Anderson, Soft Tempest: Hidden Data Transmission Using Electromagnetic Emanations, IH'98 Workshop on Information Hiding, LNCS 1525, 1998
- Markus G. Kuhn, Compromising Emanations: Eavesdropping Risks of Computer Displays, Technical Report UCAM-CL-TR-577, University of Cambridge, 2003
- Ross Anderson & Markus Kuhn, Soft Tempest: An Opportunity for NATO, Semantic Scholar, 1999
- Information Leakage via Electromagnetic Emanations and Evaluation of TEMPEST Countermeasures, ACM Digital Library, 2014
- An Introduction to TEMPEST, GIAC GSEC Practical Assignment, 2004
Papers
- Fernández et al., Deep-TEMPEST: Using Deep Learning to Eavesdrop on HDMI from its Unintended Electromagnetic Emanations, arXiv 2407.09717, 2024
- Martin Vuagnoux & Sylvain Pasini, Compromising Electromagnetic Emanations of Wired and Wireless Keyboards, USENIX Security 2009
- Screen Gleaning: A Screen Reading TEMPEST Attack on Mobile Devices, NDSS 2021
- Mordechai Guri, RAMBO: Leaking Secrets from Air-Gap Computers by Spelling Covert Radio Signals from Computer RAM, arXiv 2409.02292, 2024
- Harrison et al., A Practical Deep Learning-Based Acoustic Side Channel Attack on Keyboards, 2023
- Richard Aldrich & Christopher Murphy, The Impact of 'Tempest' on Anglo-American Communications Security and Intelligence, 1943-1970, Cryptome PDF
- Camurati et al., Screaming Channels: When TEMPEST Meets Side Channels and Wireless Security, CCS 2018
Secondary
- TEMPEST: Electronic Spying and Countermeasures, Grey Dynamics, 2025
- TEMPEST in a Software Defined Radio, Hackaday, 2017
- Markus Kuhn, Soft Tempest FAQ, Cambridge University
- Joel McNamara, Secrets of Computer Espionage: Tactics and Countermeasures, 2003
- Peter Wright, Spycatcher, 1987